Quick Summary: Spam bots don’t always use your frontend checkout page. Many hit the WooCommerce REST API directly, bypassing CAPTCHAs and password protection. The fix is a multi‑layer defence combining Cloudflare, checkout restrictions, rate‑limiting, and anti‑spam tools.
Result: Spam orders drop from hundreds to zero in a matter of hours. This guide shows you how to implement these defenses based on real client cases.
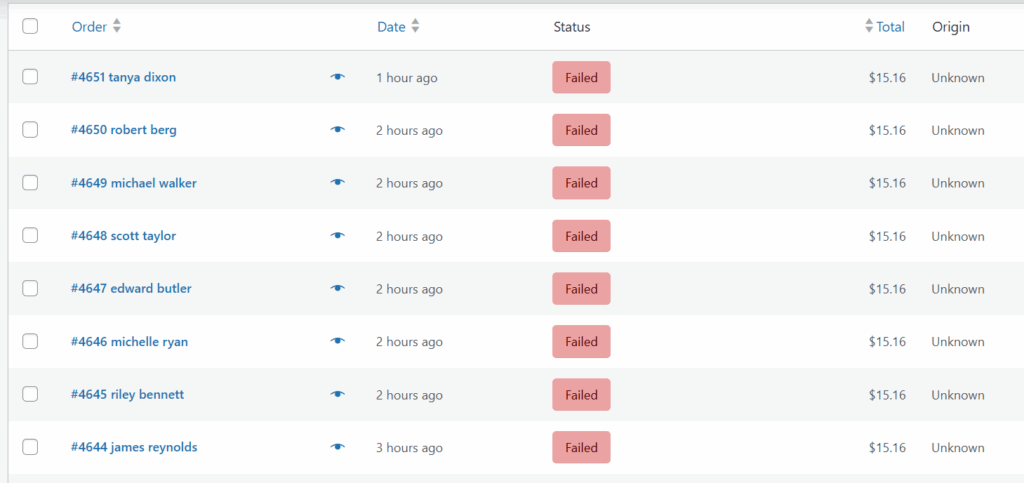
You wake up, check your store dashboard, and see 50, 100, or even more new orders waiting. For a second, you’re elated… until you see that all of them are Failed. And they are for the same product. And they are using free email accounts like “[email protected]” or “[email protected]”.
Spam orders. They’re not just annoying; they clog your database, mess up your sales reports, use up your server resources, slow your website, and risk getting you flagged or blacklisted by your payment processor if the attackers are testing stolen cards.
Quick Fixes: How to Stop Fake WooCommerce Orders Now
If you need an immediate solution while you’re being bombarded with fake orders, start here:
- Set up Cloudflare protection (I’m including this even though it takes at least 30 minutes to set up, because it’s critical and solves way more than just spam orders)
- Disable guest checkout (WooCommerce → Settings → Accounts & Privacy → uncheck “Allow customers to place orders without an account”)
- Install CAPTCHA / Turnstile or a honeypot plugin like CleanTalk (paid) or WP Armour (free, but you might need the paid version to protect more pages)
- Enable WooCommerce Store API Rate‑Limiting – to limit excessive requests, go to WooCommerce -> Settings -> Advanced -> Features and enable “Rate limiting Checkout block and Store API”
These steps will stop about 80% of basic spam bots. But if you’re still getting fake orders after implementing these fixes, keep reading – your spammers may be using a more sophisticated attack.
When “Secure” Stores Still Get Spam
Recently, I got an urgent message from a client, worried that their WC store had been hacked. They were getting dozens of spam orders every single day, despite having:
- Password-protected their entire WooCommerce shop with a paid plugin
- Installed Wordfence and Sucuri
As a side note, here’s something funny I’ve noticed: these issues always seem to come in groups. When one client reaches out about a problem, I can count on at least one or two more showing up with the exact same issue within a few days. Sure enough, within a couple of days, a second client reached out with a similar problem.
Time to investigate. I dove into the server logs, looking for any pattern that would explain how bots were bypassing all their security measures. And soon enough, I had my answer.
How the Attackers Are Exploiting The WooCommerce REST API
Client no. 1 – the logs were showing the largest number of requests were for URLs like:
/wp-json/wc/store/products/wp-json/wc/store/cart/wp-json/wc/store/checkout
On Client no. 2‘s site, the attackers where using a different approach:
GETrequest to a product page with?add-to-cart=… in the URL- Then immediately after adding an item to the cart, a different IP from the same botnet sends a
POSTrequest to/?wc-ajax=ppc-simulate-cart
These aren’t regular web pages you can visit. The first ones are part of WooCommerce’s Store API – a system that allows scripts to interact with your store without loading the visual website.
The ppc-simulate-cart is not standard WooCommerce; it belongs to PayPal Commerce plugin. The bots were exploiting this plugin’s AJAX function to fill the cart and trigger the checkout process.
Why You Get Fake WooCommerce Orders (Even With Security Plugins)
Most store owners don’t realize that spam bots don’t browse your website like normal customers.
They don’t click through your product pages, read descriptions, or fill out checkout forms. They’re automated scripts – programs running on autopilot that talk directly to your store’s database through unguarded doors, like the endpoints (URLs) I just mentioned, from the Store API or from payment plugins.
These endpoints or URLs must remain publicly accessible for customers to add products to the cart, but unfortunately bots abuse them.
Why password protection can fail
Many store owners password‑protect pages using a plugin. But unless your protection also applies to API requests, the Store API stays open. Bots can still submit orders without visiting the frontend. And this is exactly what happened with Client no 1, who was already using a password-protection plugin.
Why CAPTCHAs can fail
CAPTCHAs only protect forms that load in the browser. If a bot uses the API directly, then no form, no CAPTCHA.
Why security plugins can fail
Security plugins focus on login attempts, comment spam, and request blocking or rate limiting. They do not detect sophisticated API checkout abuse.
The Complete Solution That Stops WooCommerce Spam Orders
Stopping WooCommerce spam requires multiple security layers working together. Here’s what actually works based on real implementations:
0. Have a Really Good Hosting Provider (Often Overlooked)
A reliable hosting provider is a major part of preventing spam orders and other attacks, and the first line of defense. Good hosts actively monitor malicious traffic and notify you of threats (and not just try to upsell one of their services), isolate infected accounts, and keep server‑level firewalls updated and properly configured. This means many attacks are blocked before they ever reach WordPress or WooCommerce. If your hosting is slow, outdated, or lacks proper security layers, bots have an easier time overwhelming your site.
If you’re unsure how to choose a secure, well‑maintained hosting provider, see my (frequently updated) article on Recommended Hosting for Your WordPress Site, where I cover both low- and medium-cost options.
1. Implement Cloudflare Protection (The Most Important Step)
Cloudflare adds a powerful layer of bot detection before traffic even reaches your server. This was the game-changer for my clients.
After implementing Cloudflare with properly tuned settings, their spam orders went from 50 orders per day to zero – while legitimate orders continued flowing normally.
Basic setup (free plan works):
- Sign up for Cloudflare and add your domain
- Change your domain’s nameservers (Cloudflare provides instructions)
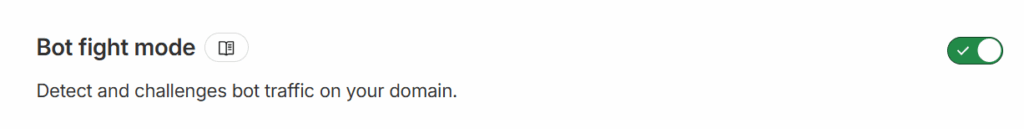
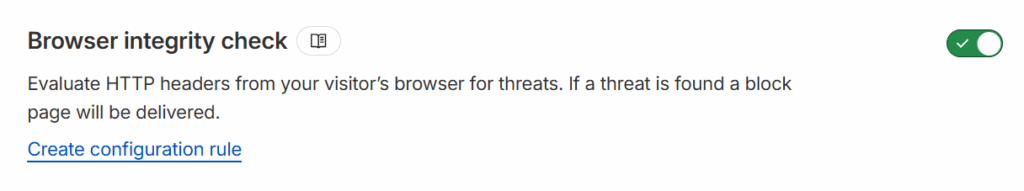
- Enable “Bot Fight Mode” and “Browser Integrity Check” under Security > Settings
- (Advanced) Set up Security Rules to block the vulnerable entry points. This requires a more advanced level; you need to figure the differences between legitimate requests and malicious requests from your logs, so that your Security Rules don’t block real users.
Finding the right balance:
The reality is every site is different. You’ll need some trial and error to find the sweet spot between blocking spammers and letting real orders through.
Critical testing step: After changing settings, always test in an incognito/private browser window. Make sure real customers can still:
- Browse products and use filters
- Add items to cart
- See cart updates
- Complete checkout
- Use Express Checkout buttons (Apple Pay, Google Pay)
If legitimate orders start getting blocked, dial back the security level slightly and tweak your Security Rules. Just keep an eye on Cloudflare’s events log for each of your custom Security Rules and see if you might have missed anything.
To access them, go to your Cloudflare’s site dashboard, Security → Security Rules
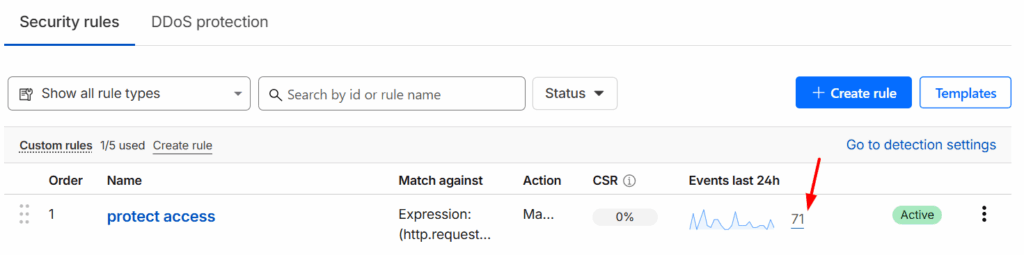
Then click on the Events for each rule → select Last 24 hours → Export.
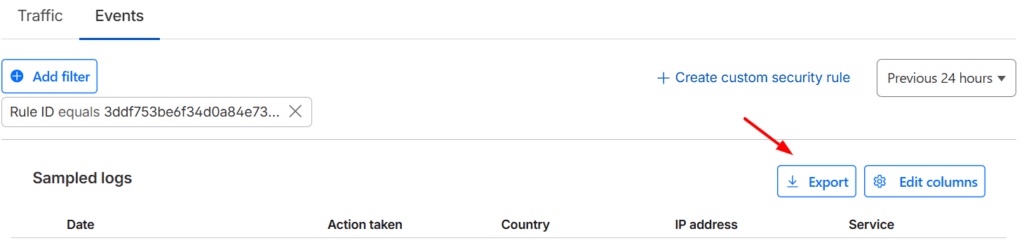
You can now go over the logs and see if there was any legitimate looking traffic that got blocked or bad bots that are getting through. Or feed the logs into an AI assistant and have it do this. But you still need to double check their findings and make sure they are accurate, don’t just rely on what the AI chatbot is saying.
2. Disable Guest Checkout (Optional but Effective)
Where to configure: WooCommerce → Settings → Accounts & Privacy
Uncheck:
- “Allow customers to place orders without an account”
Check:
- “Allow customers to create an account on the ‘My account’ page”
- “Allow customers to create an account during checkout”
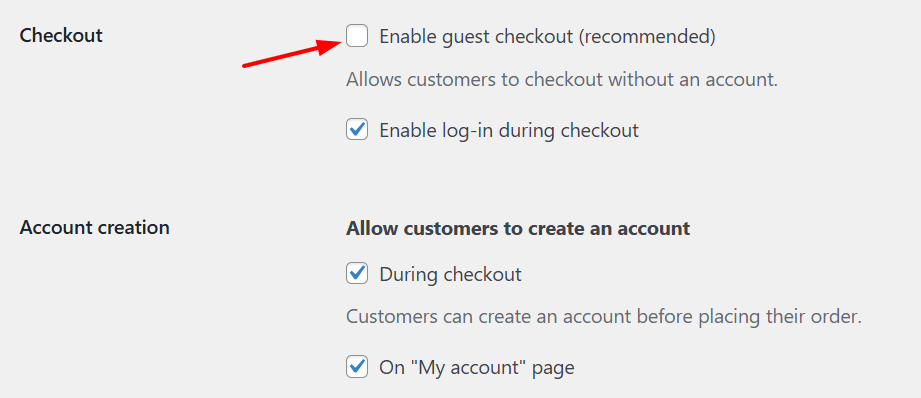
Why this works: The guest checkout page is a bot’s favorite target. It’s a simple, predictable, single-page form, making it perfect for automated spam, especially for card testing (where bots place hundreds of small orders to test stolen credit card numbers).
When you disable guest checkout, you force all potential spammers to pass through your registration form. This allows you to use more targeted anti-spam tools at that single point – see the recommendations below on using CAPTCHA, a honeypot and email verification.
Important limitations:
- Sales Impact: Forcing registration will add friction for your real customers. It’s a known cause of cart abandonment. You must decide if this conversion rate trade-off is worth the reduction in spam.
- Security Limitation: This step alone is not a complete fix. It will only deter the simple, lazy bots. A sophisticated bot can still be programmed to fill out a registration form.
3. Add Turnstile / CAPTCHA or Honeypot to Registration & Checkout
Think of CAPTCHAs and honeypots as small tests that help your site separate humans from bots. CAPTCHAs ask visitors to prove they’re real people. Honeypots are invisible form fields that only bots fill out. When a bot completes the hidden field, the submission is automatically rejected – all invisible to real users. And Turnstile is Cloudflare’s modern, privacy-friendly alternative to reCAPTCHA.
Install one of these plugins:
- Cloudflare Turnstile (recommended) — privacy‑friendly, fast
- Google reCAPTCHA — widely supported and low friction
- WP Armour Honeypot — lightweight, works invisibly
- CleanTalk — paid but powerful
Note: This protects the frontend forms, not the API itself. But many bots still attempt normal form submissions.
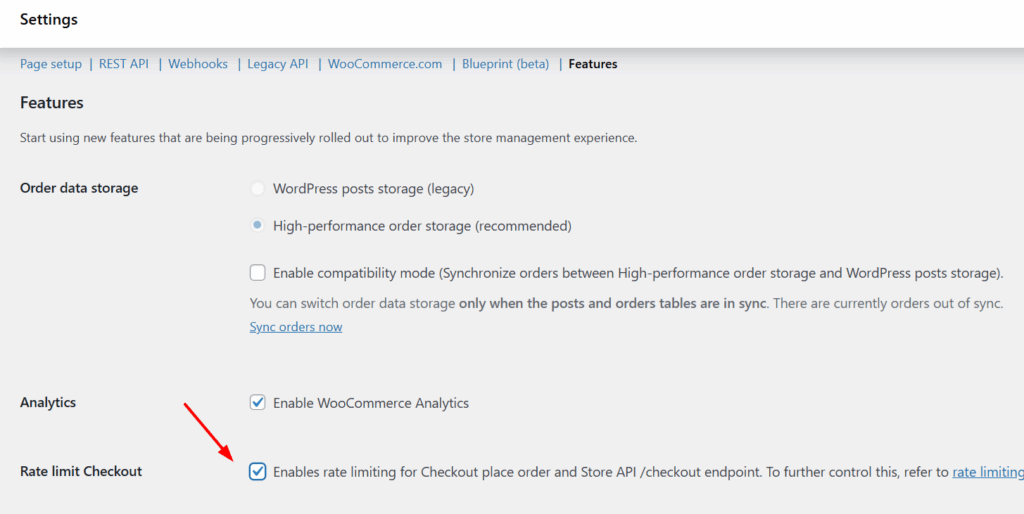
4. Enable WooCommerce Store API Rate‑Limiting
WooCommerce has started to include support for limiting the number of excessive request, such as those from card testing or spam attacks. By default, the setting is off.
You can enable rate limiting for Checkout (place order and endpoint) by going to WooCommerce -> Settings -> Advanced -> Features and enabling “Rate limiting Checkout block and Store API“. The default limit is maximum 25 requests per 10 seconds.
5. Ongoing Monitoring
Make these checks part of your weekly or monthly routine::
- Review failed orders
- Check for patterns (IP, email, country)
- Delete spam orders to keep the database lean
- Monitor server logs for unusual traffic spikes or activity
- Review Cloudflare analytics
- Keep WordPress, WooCommerce, and all plugins updated
6. Additional Security Measures
Optional but helpful:
- Add a behaviour‑based anti-fraud plugin. Just keep in mind that, in some cases, these can produce false positives and block legitimate orders.
- Enable email verification for new accounts to stop bots that auto‑register. This is not default WC functionality, you need a plugin like Customer Email Verification for WooCommerce.
- Disable free shipping unless necessary
The Bigger Picture: Security Is Ongoing
Here’s the truth: spammers are constantly evolving. What works today might need adjustment tomorrow.
Today, they’re exploiting the Store API. Next week, they might find a vulnerability in a plugin. Next year, who knows?
This is why staying ahead of these threats isn’t a one-time fix – it’s an ongoing process.
Even with Cloudflare, Sucuri, Wordfence or any other firewall/monitoring app you might use, you still need to:
- Monitor your store regularly
- Adjust security settings as needed
- Keep your plugins updated
- Review security logs for unusual activity
Need Help Securing Your WooCommerce Store?
As a freelance WordPress developer who’s been building and securing WooCommerce stores for over two decades, I offer custom maintenance and security plans that include:
✓ Cloudflare setup and optimization
✓ Proactive threat monitoring and prevention
✓ Regular security audits , updates and optimization
…and more.
